Mary Madison, RN, RAC-CT, CDP
Clinical Consultant – Briggs Healthcare®
Verizon just released its 2018 Protected Health Information Data Breach Report (PHIDBR). “The goal of this report is to inform security practitioners in the healthcare industry—and anyone else who has a level of responsibility for the protected health information (PHI) of their employees—about the threats that they face.”
Here are “some quick facts about this report and what they tell us about the issues that the healthcare industry as a whole needs to address:
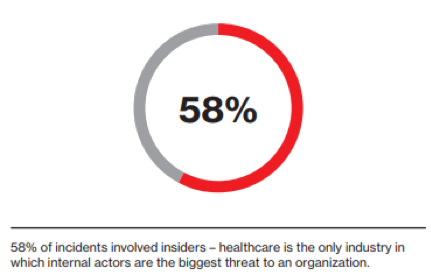
- 58% of incidents involved insiders—healthcare is the only industry in which internal actors are the biggest threat to an organization
- Medical device hacking may create media hype but the assets most often affected in breaches are databases and paper documents.
- Ransomware is the top malware variety by a wide margin. 70% of incidents involving malicious code were ransomware infections
- Basic security measures are still not being implemented. Lost and stolen laptops with unencrypted PHI continue to be the cause of breach notifications.”
The 20-page report contains a great deal of information that is critical for all nursing home and senior living community management and owners to review then act on before their community suffers a data breach – before it’s too late.
One of the many striking results of this report (to this author) was the length of time before discovery was made of a data breach and the likely motive:
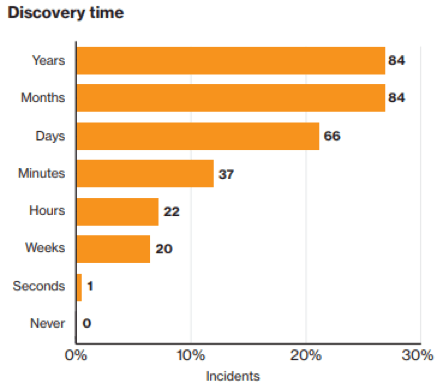
“The elephant in the figures is the number of incidents where the discovery was measured in months or years. A trip back into the dataset shows that half (51%) were employees misusing privileges. Once the inappropriate actions were discovered, often the behavior can be traced back for several years. A surprising finding was that the motives, when known, were more likely to be financial in nature as opposed to fun or curiosity.”
The Verizon PHIDBR offers these recommendations:
- “A comprehensive review and ongoing audits of access rights to sensitive data to ensure ease of access to front-line medical providers, yet reduce authorization creep within organizations is essential.
- Establishing a proactive policy of building security into any and all implementations is vital to getting ahead of what could be an increasing threat in the future.
- A formalized policy specific to testing and vetting of connected medical devices as well as third-party legal reviews of contracts should be developed.
- Focusing on resiliency and availability in regards to IoT implementations as well as integrity or confidentiality is important.
- Tabletop exercises and planning around environmental threats (severe power outages, natural disasters) or device malfunctions to ensure that backup plans exist to continue to treat patients should be planned and conducted.
- An overall incident response (IR) plan should be established and include both internal stakeholders as well as external partners in areas of legal guidance and forensic investigative assistance. The ability to react quickly and efficiently can often make a difference in the level of impact an incident has on an organization. Tabletop exercises and walk-throughs must be conducted to gauge the ability to execute what has been documented.
- Improvements in detection of potential security incidents and/or data breaches are a core component of the overall risk management program. Validate your implementation of basic security fundamentals as we continue to see data breaches that have simple and cheap corrective actions associated with them. Then focus on more advanced detection and response capabilities.”